The VMware Horizon Access Point greatly reduces the amount of resources needed for the redundant or non-redundant Horizon Environment.
Previously when deploying Security Server, a single Security Server needed to be sized as a Connection Server which is 4vCPU and 12GB of RAM. If you combine that with the Connection Server that the Security Server is paired with, the Connection Server is once again 4vCPU and 12GB of RAM. If this was a redundant environment your Connection Server and Security Server infrastructure tallies up to 24vCPU and 72Gb of RAM (2 Internal Connection Servers, 2 External Connection Servers and 2 Security Servers all sized at 4vCPU and 12GB of RAM).
The Horizon Access Point is a SUSE Linux Enterprise Server (SLES) appliance that is imported into your VMware vSphere environment and serves as a proxy to the internal URL to access the Horizon environment.
Let’s take a look at the resources required with a redundant environment (that tallies up to 12vCPU and 32GB of RAM — 2 Connection Servers and 2 Access Point Appliances). You can now save 40GB of RAM to be used elsewhere. In addition, the Horizon Access Point can port share BLAST HTML5 on port 443 as opposed to having to use 8443 when the Security Server is in use.
So how do we deploy the Access Point?
Previously there was an Access Point Deployment Utility. Unfortunately, this VMware Fling has been deprecated and the download is no longer available.
The Solution:
The Horizon Access Point via a PowerShell script.
Mark Benson, a VMware SA, has created these PowerShell scripts that automate the deployment of the Horizon Access Point or VMware Unified Access Gateway. Don’t be scared off by the length of the instructions, it’s easier than it looks!
It’s recommended that you deploy using PowerShell as opposed to manually. Deploying manually often results in the HTML5 interface reporting a 404 Page Not Found message.
Here are the steps to prepare the environment for the Access Point appliance:
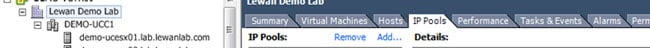
Before you import anything or use any utility, you will need to create an IP Pool or Network Protocol Profile on the designated VM port group we are going to connect to the virtual appliance. In the Access Point appliance, we do not specify a netmask or gateway. The IP Pool or Network Protocol Profile provides this for the appliance to use.
- Create and IP Pool or Network Protocol Profile in your vSphere environment.
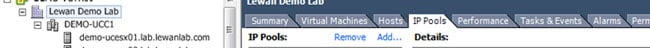
- In your vSphere client, select your datacenter object.
- Click on IP Pools tab.
- Click Add.

- Give the IP Pool a descriptive name and plug in the subnet info if it is a /24 or not and gateway address.

- Click on the Associations tab and specify the VM port group that this IP Pool is associated with.
- Download apdeploy-290-v2.zip (this PowerShell will work with all older versions of the Access Point/Unified Access gateway appliances).
- Download the VMware OVF Deployment Tool. This will be used to deploy the OVF with the parameters from the PowerShell script.
- Install the VMware OVF Deployment Tool which is a Next, Next, Next and Finish
- Extract apdeploy-290-V2.zip and edit the ap1-basic.ini.
Here is an example of the .ini using a Single Network Deployment. Change the information to fit your environment for the sections that are not marked with a #.
[General]
#
# Access Point virtual appliance unique name (between 1 and 32 characters).
# If name is not specified, the script will prompt for it.
#
name=Appliance Name in vSphere (exact case as you would like for it to be seen)
#
# Full path filename of the Access Point .ova virtual machine image
# The file can be obtained from VMware
#
source=C:\apdeploy-280-v3\euc-access-point-2.8.0.0-4689690-OVF10.ova
#
# target refers to the vCenter username and address/hostname and the ESXi host for deployment
# Refer to the ovftool documentation for information about the target syntax.
# See https://www.vmware.com/support/developer/ovf/
# PASSWORD in upper case results in a password prompt during deployment so that passwords do not need
# to specified in this .INI file.
# In this example, the vCenter username is administrator@vsphere.local
# the vCenter server is 192.168.0.21 (this can be a hostname or IP address)
# the ESXi hostname is esx1.myco.int (this can be a hostname or IP address)
#
target=vi://administrator@vsphere.local:PASSWORD@vctr01.lab.lewanlab.com/Lewan Demo Lab/host/DEMO-UCC1/esx01.lab.lewanlab.com
#
# vSphere datastore name
#
ds=Datastore name (case sensitive)
#
# vSphere Network names. A vSphere Network Protocol Profile must be associated with every referenced network name. This specifies
# network settings such as IPv4 subnet mask, gateway etc.
#
netInternet=LAB
netManagementNetwork=LAB
netBackendNetwork=LAB
#
# Setting honorCipherOrder to true forces the TLS cipher order to be the order specified by the server. This can be set on
# Access Point 2.7.2 and newer to force the Forward Secrecy ciphers to be presented first to improve security.
#
honorCipherOrder=true
ip0=172.16.1.62
dns=172.16.1.2
[Horizon]
#
# proxyDestinationUrl refers to the backend Connection Server to which this Access Point appliance will connect.
# It can either specify the name or IP address of an individual Connection Server or of a load balanced alias to connect
# via a load balancer in front of multiple Connection Servers.
#
proxyDestinationUrl=https://internalhorizon.lewanlab.com
proxyDestinationUrlThumbprints=sha1:5f 0a 31 2f 67 0f d2 fe 5d a1 da 3b ea 1f 47 38 72 c9 3b d2
tunnelExternalUrl=https://externalhorizon.lewanlab.com:443
blastExternalUrl=https://externalhorizon.lewanlab.com:443
pcoipExtenalUrl=172.16.1.5:4172
NOTE: The user importing the appliance has to be administrator@vsphere.local. The hierarchy objects in the VI string are @vcenter.fqdn.com/Datacenter Object/host/Cluster Object/Host Object. All of this is case sensitive as it shows in your vSphere client. If case is mismatched the script will not be able to find it.
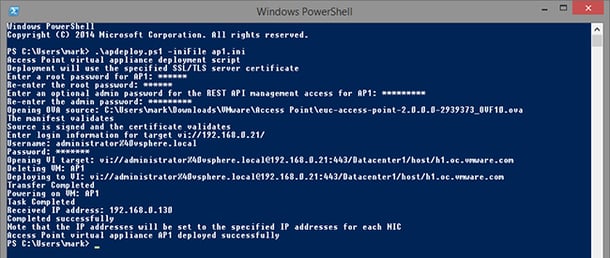
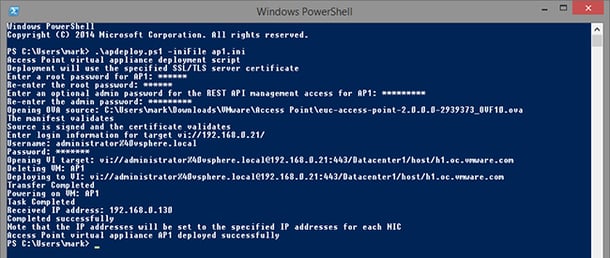
- Once the ap1-basic.ini is prepped, it is ready to deploy. Open a PowerShell as admin on the machine where the VMware OVF Deployment Tool is installed.
- Set the user execution of PowerShell to unrestricted with this command:
set-executionpolicy -scope currentuser unrestricted
- Change the directory to the location of the ap1-deploy.ini and the ps1 scripts and unblock the PowerShell script with this command:
unblock-file -path .\apdeploy.ps1
- Execute the script:
\apdeploy.ps1 -iniFile ap1-deploy.ini
NOTE: The script will ask for the root, admin, and rest ap1 account passwords to be used.
- Once it’s done deploying, it will say “Completed successfully” and the appliance will automatically boot.
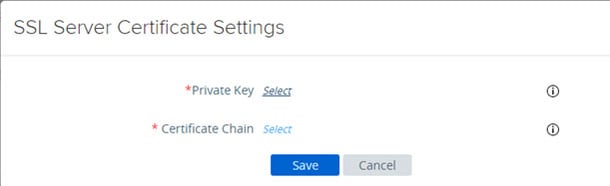
We’re not done yet, now we need to prepare the certificate for the appliance to use:
- Download OpenSSL and extract it to a location where you are going to prepare the certificate.
- Export your current certificate from your Security Server with the entire chain and encrypt the .pfx with your designated password.
- Copy the .pfx into the C:\OpenSSL-Win32\bin.
- Here are the two commands that will generate the pem and certchain.pem
openssl pkcs12 -in MyCert.pfx -out MyCertchain.pem –nodes
openssl pkcs12 -in mycertchain.pfx -nodes -nocerts -out mycertkey.pem
NOTE: It’s critical that the certificate installation occur using Firefox or Google Chrome. If you use Internet Explorer the fields don’t change and the dialogue will ask you to select a file.

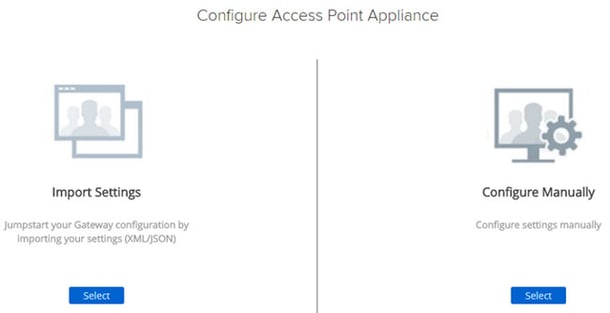
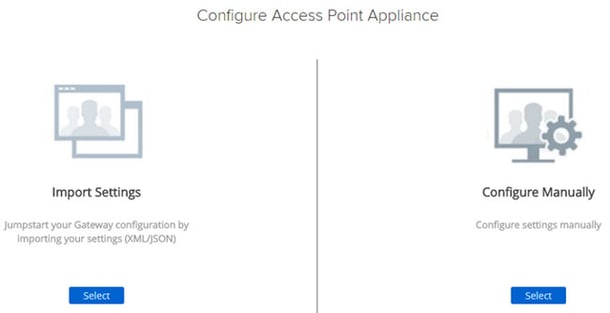
- Point your browser to https://IPADDRESSOFAPPLIANCE:9443/admin.
- Login as the admin user and the password specified earlier.
- Select Configure Manually.
- In the SSL Server Certificate Settings, click the gear icon.

- Select the pem for the private key and mycertchain.pem for the certificate chain.
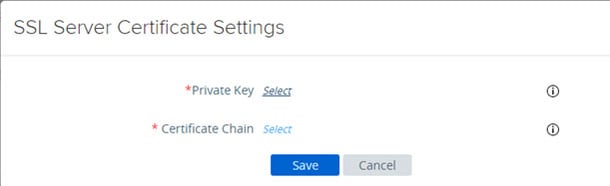
- Save.
- Reboot for good measure.
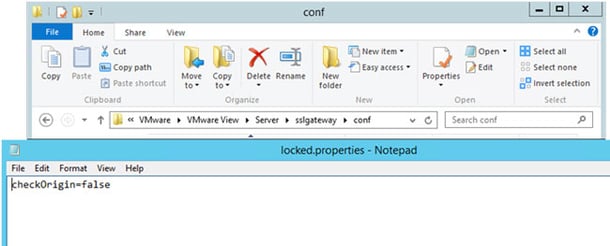
- Now on your connection server under C:\Program Files (x86)\VMware\VMware View\Server\sslgateway\conf create a file called properties and within this file, type a line called checkOrigin-false.
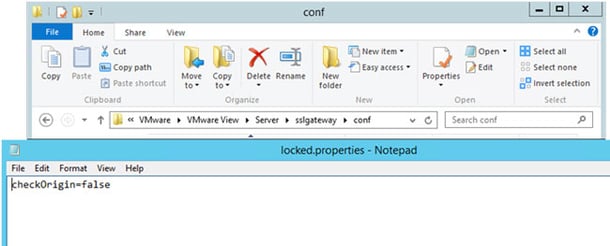
NOTE: This security feature is enabled by default and prevents the page from loading unless specific URLs are used. We need to disable this for HTML5 through the Access Point/Unified Access Gateway to function. More on disabling it here.
Now we need to disable the PCoIP Secure Gateway and Secure Tunneling on the Connection Servers (the Secure Tunneling should be handled through the appliance).

- Logon to the Horizon Admin console https://connectionservername/admin
- Under View Configuration à Servers à Connection Servers select Connection Server(s) and click Edit.
- Uncheck HTTP(S) Secure Tunnel, PCoIP Secure Gateway and Blast Secure Gateway.
- Reboot the Connection Server and now we are ready to test.
To Test:
From an external internet source go to https://externalhorizonurl.com.

Lewan Technology is a VMware Premier Solutions Partner headquartered in Denver, Colorado, with certified technical professionals in server virtualization, business continuity, desktop virtualization, hybrid cloud, management operations and software-defined storage. Our team of consultants is your strategic partner to keeping IT relevant and enabling components of your business -  !
!