Here at Lewan HQ we have a robust internal lab where we demo solutions and hardware for customers and train our team. The lab gives us the opportunity to actually touch and test products before evaluating or installing onsite for clients.
As part of our lab, we have a complete VMware Horizon Enterprise deployment with all the bells and whistles and integrated technologies from our other hardware and software partners. This allows us to do expanded testing beyond what the primary manufacturers can do.
Today that was integration testing for VMware Horizon 7, and I learned a few things I wish I'd known before I started. I hope this post saves you the time I spent troubleshooting cryptographic protocol issues and makes for a more seamless upgrade of your infrastructure!
Here's how it went for me:
VMware Horizon 7 has been out for about a month now, and I decided it was time to upgrade the lab. I read the docs, made my backups and pulled the trigger. Every single component upgraded in place without errors. I applied my new Horizon 7 license. So far, so good.
I launched a desktop from my jump-box and it connected. Excellent, success!
Not so. A couple desktops later, I couldn't connect to anything. I investigated and discovered that I was getting SSL certificate errors talking to my vSphere 5.5 vCenter (but not the vSphere 6.0 one). I double and tripled checked my certs and all of them looked ok.
Long story short, it turns out Horizon 7.0 had disabled TLS v1.0 across all components (not to mention SSLv3, SSLv2 and all lesser variants). This broke communication with vCenter 5.5, which doesn't support 1.1+ out of the box.
I could handle that with a common hack on Composer and some ADSI Edit fiddling to turn on the client side so that the Managers can talk to vCenter.
But the next issue was that my connection to the Security Server was broken. We use a Citrix NetScaler VPX to do content switching in front of a number of lab URLs, with the HTTP/S portion of the Security Server being part of that. Well, NetScaler VPX doesn't support TLS 1.1+ for back end services. So I had to do more ADSI Edit fiddling to turn on the server side TLS v1.0 support on the Security Server.
Fortunately, our Teridichi based P25 and P45 thin clients were happy with the new environment and just worked, but I do have a pretty current firmware on them (your mileage may vary).
Unfortunately that's where the thin clients also stopped being happy. The rest, including the Windows embedded versions, all failed to connect or hold a session, so I found myself doing more ADSI Edit work to turn on the server side TLS v1 for the Managers.
I got all the TC's to connect and enumerate desktops. Most however still wouldn't hold a session to the new View Agent. So next, I had to go into Group Policy Editor and pcoip.adm to turn on TLSv1 on the agent.
Finally, everything was working in the lab again, but it took a lot of time researching, troubleshooting and digging around for answers.
The good news for you though, is that most of that pain can be avoided by making sure your infrastructure is ready before you do the upgrade. So here is the info you need to enable TLSv1. Make sure you're ready before you upgrade!
Enable TLSv1 to vCenter from Managers
Enable TLSv1 to vCenter from Composer
Enable TLSv1 to Manager or Security Server from Clients
Enable TLSv1 to View Agent from Clients
As always,  for an assessment, help managing the upgrade or planning a hardware refresh!
for an assessment, help managing the upgrade or planning a hardware refresh!
Lewan Technology is a VMware Premier Solutions Partner headquartered in Denver, Colorado, with certified technical professionals in server virtualization, business continuity, desktop virtualization, hybrid cloud, management operations and software-defined storage.
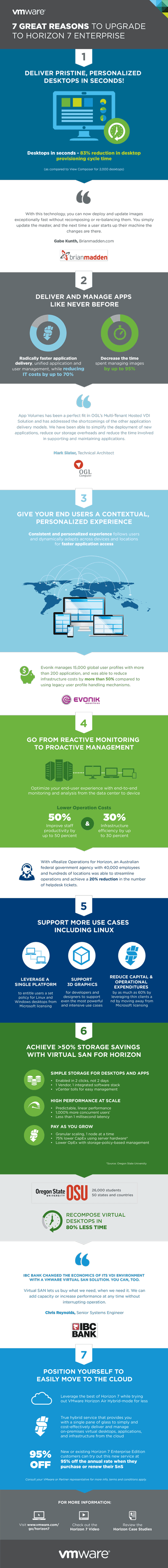
Still considering whether you should upgrade to VMware Horizon 7? Here are 7 reasons why you should make the jump: